There’s a simple, almost uncomfortable truth at the core of Bitcoin:
Whoever controls the seed phrase controls the money.
At an individual level, that’s empowering. It means you don’t need a bank. No permission. No middleman. Just you and your keys.
But scale that idea up to a nation-state—and it becomes something else entirely.
Now the question isn’t just about security. It’s about power, sovereignty, and trust at a global level.
If a country were to hold billions (or even trillions) of dollars in Bitcoin, how would it secure that wealth? Who would hold the keys? And more importantly—how do you build a system where no single person, institution, or even government faction can take control?
This is where Bitcoin stops being a financial tool and becomes infrastructure.
The Problem: Seed Phrases Don’t Scale
A seed phrase—typically 12 or 24 words—is the master key to a Bitcoin wallet. Lose it, and the funds are gone forever. Expose it, and anyone can take everything instantly.
For individuals, this is manageable. For institutions, it’s risky. For countries, it’s unacceptable.
A nation cannot rely on:
- One person
- One device
- One location
- One point of failure
Because any one of those becomes a vulnerability:
- A rogue insider
- A cyber breach
- A political shift
- A physical attack
At sovereign scale, the seed phrase model must evolve into something far more sophisticated.
The Solution: Eliminate Trust, Don’t Assign It
Most people think the solution is choosing the “right” person or entity to trust.
That’s not how serious systems are designed.
Instead, nations aim to eliminate the need for trust entirely.
They do this by distributing control across multiple layers—technical, geographic, and human—so that no single actor can compromise the system.
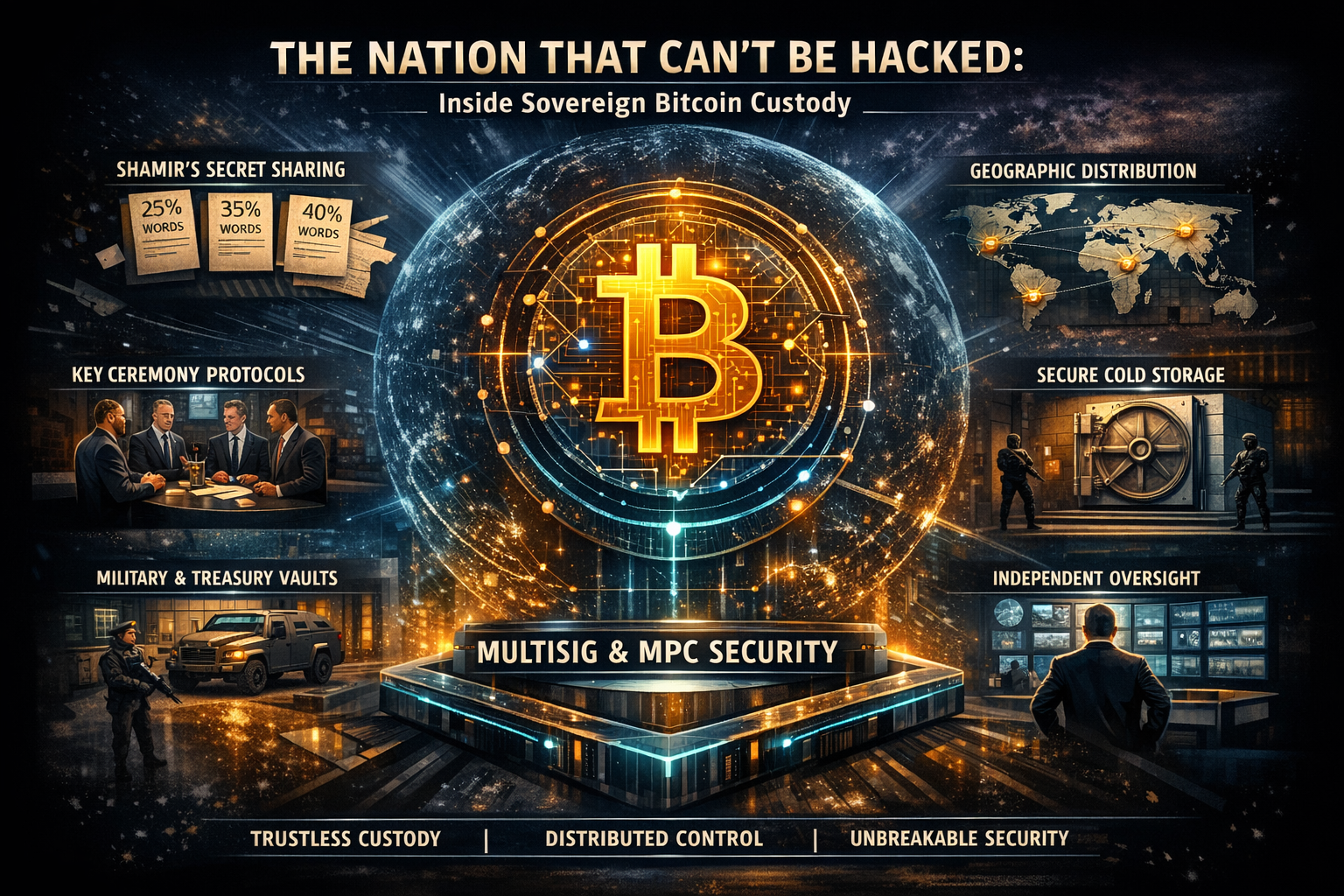
Layer 1: Multi-Signature Wallets (Shared Authority)
The first evolution beyond a single seed phrase is the use of multi-signature wallets, or “multisig.”
Instead of one private key controlling funds, multiple keys are required to authorize a transaction.
For example:
- 9 total key holders
- 5 signatures required to move funds
This is called a 5-of-9 multisig structure.
What this achieves:
- No individual can act alone
- Compromise of one or two keys doesn’t matter
- Decisions require coordination
This mirrors real-world governance. Just as major decisions in government require multiple approvals, so do Bitcoin transactions.
Layer 2: Threshold Cryptography (MPC)
Multisig is powerful, but it still relies on discrete keys.
A more advanced approach is Multi-Party Computation (MPC), where:
- A private key is never fully assembled
- Each party holds only a fragment
- Transactions are signed collaboratively without revealing the full key
This creates an even deeper layer of protection:
The key doesn’t exist in one place—ever.
For a nation, this is ideal. It reduces the attack surface dramatically and ensures that even insiders don’t fully control the system.
Layer 3: Shamir’s Secret Sharing (Seed Fragmentation)
Even when seed phrases are used, they are never stored intact.
Instead, they’re split using Shamir’s Secret Sharing.
Here’s how it works:
- A seed phrase is divided into multiple “shares”
- Only a subset is required to reconstruct it
Example:
- 10 total shares
- Any 4 can rebuild the seed
This means:
- No single location holds the full secret
- Theft requires coordinated access to multiple shares
- Loss of some shares doesn’t destroy access
It’s redundancy and security at the same time.
Layer 4: Geographic Distribution
Now comes the physical dimension.
Key shares and signing devices are distributed across:
- Different cities
- Different regions
- Sometimes different countries
A sovereign setup might include:
- A central bank vault
- A treasury-controlled facility
- A military-secured site
- An allied jurisdiction
- A neutral international location
Think about what this does:
To compromise the system, an attacker would need to:
- Breach multiple secure facilities
- In multiple jurisdictions
- Possibly across different continents
At that point, the cost of attack becomes impractical.
Layer 5: Hardware Isolation (Cold Storage)
All of this is reinforced with air-gapped systems:
- Devices that never connect to the internet
- Hardware Security Modules (HSMs)
- Cold storage wallets locked in vaults
These are often protected like gold reserves—physically guarded, monitored, and controlled.
This mirrors how institutions like the Federal Reserve secure physical assets—but adapted for digital value.
Layer 6: Human Distribution (Controlled Trust)
Even with all the technology, humans are still part of the system.
The difference is how they’re used.
Instead of giving full control to one person, responsibility is distributed among:
- Treasury officials
- Central bank cryptographers
- Intelligence or defense representatives
- Independent oversight members
Each holds:
- A key
- A share
- Or access to a signing process
No one person has enough power to act alone.
The Ceremony: Moving Funds Is an Event
Accessing sovereign Bitcoin isn’t a casual action. It’s a ceremony.
A real-world key ceremony might involve:
- Multiple parties traveling to secure sites
- Identity verification (biometric + multi-factor)
- Air-gapped devices used for signing
- Independent observers and auditors
- Full documentation and recording
This process introduces intentional friction.
Why?
Because speed is not the goal. Security is.
This is closer to nuclear launch protocols than banking transactions.
Optional Layer: Institutional Custodians
Some nations may incorporate regulated custodians such as:
- Coinbase Custody
- BitGo
- Fireblocks
These firms offer:
- Institutional-grade security
- Insurance coverage
- Operational simplicity
But they introduce a tradeoff:
Convenience vs Sovereignty
A country that relies too heavily on third-party custody risks:
- Regulatory pressure
- Account freezes
- External influence
So most serious strategies favor a hybrid model:
- Internal control at the core
- External services as support—not authority
The Real Question: Who Do You Trust?
This is where the conversation becomes philosophical.
At the individual level, Bitcoin asks:
Do you trust yourself?
At the national level, it asks:
Can you trust anyone?
The answer becomes:
You don’t. You design a system where trust is unnecessary.
The Hidden Risks
Even the most advanced cryptographic system cannot eliminate all risk.
There are three that remain:
1. Internal Collusion
If enough key holders conspire, they can move funds.
2. Political Change
A new regime could gain control over key holders and infrastructure.
3. Legal Coercion
Governments—or foreign powers—could force participants to comply.
This is why sovereign Bitcoin custody is not just technical.
It is:
- Political
- Legal
- Social
Bitcoin as National Infrastructure
At this level, Bitcoin begins to resemble something familiar:
Gold reserves.
Historically, nations stored wealth in vaults—guarded, audited, and distributed.
Bitcoin replaces:
- Physical storage → cryptographic control
- Armed guards → mathematical security
- Vaults → distributed key systems
But it also introduces something new:
Portability without permission.
A nation can move billions across the world in minutes—without relying on institutions like the International Monetary Fund.
That changes the balance of power.
A Shift in Sovereignty
Traditional finance relies on:
- Central banks
- International systems
- Intermediaries
Bitcoin flips that model.
Control moves from:
- Institutions → cryptography
- Agreements → code
- Trust → verification
For nations, this creates a new kind of sovereignty:
Digital monetary independence.
Real-World Glimpses
We’ve already seen early examples.
Countries experimenting with Bitcoin are beginning to explore:
- National reserves
- Custody frameworks
- Regulatory alignment
While the full sovereign custody model is still evolving, the trajectory is clear:
Bitcoin is not just an asset.
It’s becoming part of national strategy.
The Endgame: A Nation That Can’t Be Hacked
So what does the final system look like?
Not a vault. Not a bank. Not a single authority.
But a network:
- Distributed keys
- Distributed people
- Distributed power
Where:
- No one person can act alone
- No single breach can compromise funds
- No external entity can seize control
In this system:
Ownership is enforced by math, not authority.